
How does UVA Athletics handle a sexual assault accusation internally?
I’ve got an inquiry in to University Communications at the University of Virginia on the process for handling a sexual assault accusation against a student-athlete.

I’ve got an inquiry in to University Communications at the University of Virginia on the process for handling a sexual assault accusation against a student-athlete.
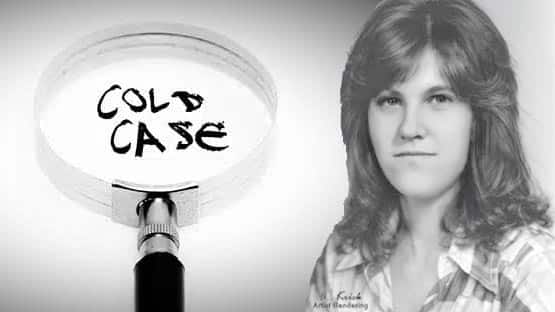
Remains found in Boca Raton, Fla., in 1978 have been traced back to a missing Harrisonburg woman whose death has now been ruled a homicide.

Solar can save Virginia farms if state and local government gets out of the way.
Our MAGA Sixth District congressman, good ol’ Ben Cline, commented on the proposed Augusta County ICE detention facility at something called a City Elders town hall in Staunton last week.

Regarding the good fortune of the valorous Kash Quixote in the fearful and never imagined sally of thwarting election fraud, along with other vomitous events worthy of joyful remembrance.

The UVA Health University Medical Center has been designated as a Level 1 adult trauma center by the Virginia Department of Health.

If you’re trying to “rank” in ChatGPT the same way you rank in Google, you’re going to have a bad quarter. That’s not my take. It’s the pattern a lot of marketers are bumping into right now, and it’s one a top marketing agency, Relevance, has been flagging in its recent research and client-facing visibility…

Seven House Democrats voted with the 220-207 majority that passed a new funding bill for the Department of Homeland Security, which includes $10 billion for ICE.

Virginia home sales were up 7.3 percent in December, according to the December 2025 Virginia Home Sales Report released by the Virginia Association of REALTORS® on Thursday.

A new congressional report has it that U.S. families spent $1,625 more on daily living things due to inflation, and that’s not counting what happens if Europe responds to Donald Trump’s threats to Greenland by pulling the rug out from under the dollar.
Our content is free to read, but we do have bills to pay. Pitch in and help us keep the community informed.